A major cross-chain exploit has shaken decentralized finance after LayerZero confirmed that the $290 million breach of KelpDAO stemmed from a targeted infrastructure attack tied to a suspected North Korean cyber unit.
The incident took place on April 18, when attackers drained 116,500 rsETH tokens, valued at roughly $292 million, from KelpDAO’s LayerZero-powered bridge. The event is now the largest DeFi exploit reported this year, based on data shared by the protocol and onchain investigators.
LayerZero stated:
"Preliminary indicators suggest attribution to a highly-sophisticated state actor, likely DPRK’s Lazarus Group, more specifically TraderTraitor."
🚨 $280M KelpDAO Hack, Who To Blame?
— HodlFM (@Hodl_fm) April 20, 2026
The rsETH bridge exploit looks less like a smart contract failure and more like a decentralization failure.
If one compromised @LayerZero_Core DVN node was enough to push a fake message through, then calling this a “Decentralized Verifier… pic.twitter.com/JaKSNJUNQi
Attack focused on infrastructure, not protocol code
LayerZero’s findings show that the attacker did not exploit a vulnerability in the protocol itself. Instead, the breach targeted the infrastructure layer that supports transaction verification.
The attacker gained access to the list of remote procedure call (RPC) nodes used by LayerZero Labs’ decentralized verifier network (DVN). These nodes act as data providers that help confirm cross-chain transactions.
Two RPC nodes were compromised. Malicious binaries replaced legitimate software on those nodes. The altered nodes sent a forged transaction message to the verifier while continuing to report normal data to all other systems. This selective behavior kept internal monitoring tools unaware of the manipulation.
The attacker also launched a distributed denial-of-service attack against uncompromised RPC nodes. This forced the DVN to rely on the poisoned nodes during the verification process.
As a result, the DVN confirmed a transaction that never occurred onchain. The KelpDAO bridge then released funds to the attacker.
Single verifier setup exposed critical weakness
LayerZero placed responsibility on KelpDAO’s configuration choices. The rsETH bridge operated under a 1-of-1 DVN setup, which meant only one verifier confirmed transactions.
"Operating a single-point-of-failure configuration meant there was no independent verifier to catch and reject a forged message," the company stated.
LayerZero had previously recommended a multi-DVN setup with redundancy. Such a structure would require consensus across multiple independent verifiers. That design would have blocked the attack even if one verifier had failed.
Despite those recommendations, KelpDAO maintained a single verifier configuration. That decision allowed the forged message to pass without challenge.
LayerZero emphasized that its protocol worked as designed. It reported "zero contagion" across other applications and assets that rely on multi-verifier setups.
Aave freezes markets as fallout spreads
The stolen funds moved quickly into the broader DeFi ecosystem. The attacker deposited rsETH into Aave V3 and used it as collateral to borrow large amounts of WETH.
This activity raised concerns about potential bad debt within the lending protocol. In response, Aave froze rsETH markets on both V3 and V4.
The rsETH markets on Aave V3 and Aave V4 have been frozen. Aave's contracts have not been exploited and this is an exploit related to rsETH.
— Aave (@aave) April 18, 2026
The freeze follows an exploit of the Kelp DAO rsETH bridge. Freezing the rsETH markets prevents new deposits and borrowing against rsETH…
Aave founder Stani Kulechov wrote on X:
"RsETH has been frozen on Aave V3 and V4, the asset does not have any borrowing power as a measure due to KelpDAO bridge exploit that happened outside of Aave."
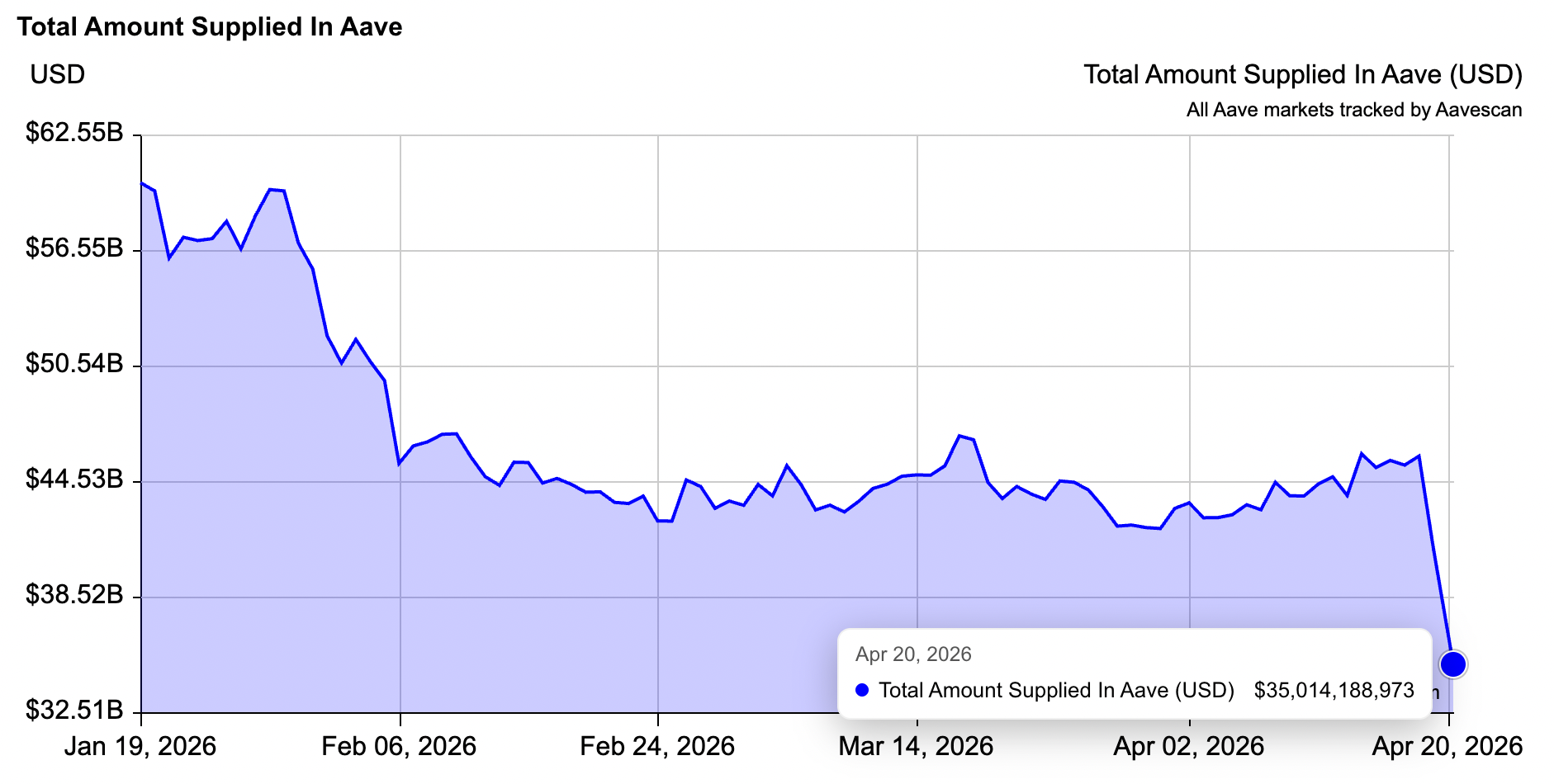
The protocol confirmed that it has no further exposure to the affected asset. Still, the reaction from users proved swift. Data from Aavescan shows more than $10 billion exited Aave after the exploit, with total supplied funds falling from $45.8 billion to $35 billion.
DeFi protocols pause bridges and TVL drops
The impact extended beyond a single platform. Several protocols paused their LayerZero-based bridges as a precaution. These included Ethena, ether.fi, Tron DAO, and Curve Finance.
Data from DefiLlama shows the total value locked across DeFi dropped about 8% within 24 hours. TVL declined from $99.5 billion on April 18 to roughly $85.4 billion.
The exploit also triggered emergency responses within KelpDAO. The protocol paused its contracts across multiple networks shortly after detecting suspicious activity. Two additional attack attempts failed after the pause, which prevented further losses.
Law enforcement and recovery efforts underway
LayerZero confirmed active cooperation with global law enforcement agencies. The company also works with security partners and tracking groups to trace the stolen funds.
The firm stated that it will no longer sign messages for any application that uses a 1-of-1 DVN configuration. It has begun outreach to projects that still rely on single-verifier setups, urging migration to multi-DVN security models.
The attacker’s tactics highlight a shift toward infrastructure-level exploits rather than direct smart contract vulnerabilities. This case combined node compromise, selective data manipulation, and network disruption to bypass safeguards.
The investigation remains ongoing. LayerZero said it will provide further updates as new findings emerge.

Disclaimer: All materials on this site are for informational purposes only. None of the material should be interpreted as investment advice. Please note that, despite the nature of much of the material created and hosted on this website, HODL FM operates as a media and informational platform, not a provider of financial advisory services. The opinions of authors and other contributors are their own and should not be taken as financial advice. If you require advice, HODL FM strongly recommends contacting a qualified industry professional.





