Security researchers at Google have revealed a sophisticated exploit framework capable of compromising iPhones and extracting cryptocurrency wallet data. The exploit kit, internally named “Coruna,” targets devices running Apple iOS versions from 13.0 to 17.2.1, according to a report from the Google Threat Intelligence Group (GTIG).
They identified five full iOS exploit chains and 23 separate vulnerabilities inside the toolkit. The vulnerabilities allow attackers to execute malicious code through web content by exploiting weaknesses in Apple’s browser engine and system components. GTIG warned that the exploit kit demonstrates how advanced surveillance-grade tools can move into broader cybercrime operations.
According to the report, the exploit does not work against the latest iOS releases and users are urged to update their devices.
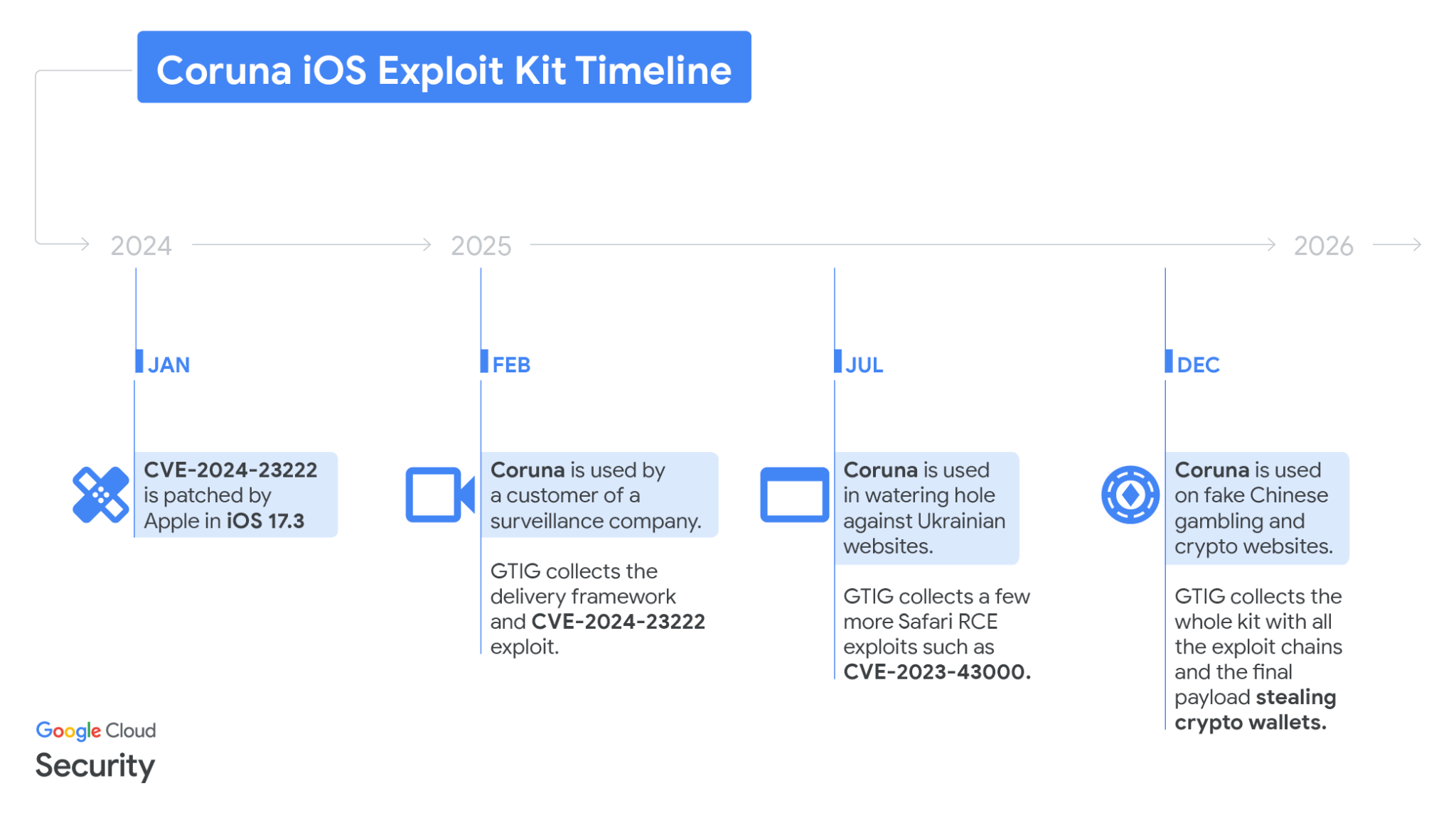
Exploit first detected in targeted surveillance activity
GTIG first observed parts of the exploit chain in February 2025 during an investigation involving a customer of a commercial surveillance vendor. The study captured elements of the attack framework embedded in a previously unseen JavaScript environment.
The framework contained code designed to fingerprint devices before exploitation. It collected device information to determine the exact iPhone model and operating system version. Once the environment matched a vulnerable configuration, the framework delivered a tailored exploit chain through WebKit.
The attack sequence relied on vulnerabilities such as CVE-2024-23222, which had previously functioned as a zero-day flaw before Apple patched it in January 2024 with the release of iOS 17.3.
The exploit chains contained extensive documentation and structured modules. Many exploits included comments written in fluent English and used advanced mitigation bypass techniques that remain uncommon in public exploit frameworks.
The campaign expanded into geopolitical and criminal operations
Later in 2025, the same JavaScript framework appeared in watering-hole attacks against Ukrainian users. GTIG linked this campaign to UNC6353, a suspected Russian espionage group.
Compromised Ukrainian websites hosted hidden frames that delivered the exploit framework to selected visitors. The sites ranged from industrial equipment portals to local service pages and retail platforms. The malicious code targeted iPhone users based on geolocation.
Investigators collected several WebKit remote code execution exploits during this campaign, including CVE-2024-23222, CVE-2022-48503, and CVE-2023-43000, before servers hosting the attack infrastructure shut down.
GTIG coordinated with Ukraine’s national cyber emergency response team to remove the compromised websites.
Fake finance and crypto websites spread the exploit kit
By the end of 2025, investigators discovered the same exploit framework across numerous fraudulent Chinese websites connected to financial services and cryptocurrency platforms.
Some pages impersonated exchanges such as WEEX and encouraged visitors to access the site from an iPhone. When an iOS device opened the page, a hidden frame injected the exploit kit regardless of the visitor’s geographic location.
This phase of the campaign appeared linked to UNC6691, a financially motivated threat actor operating from China, according to GTIG.
They retrieved hundreds of exploit samples from these sites. One configuration accidentally exposed a debug version of the framework that revealed internal code names and confirmed that developers referred to the toolkit as Coruna.
Malware searches for crypto wallet seed phrases
After exploitation succeeds, the framework deploys a loader called PlasmaLoader. The loader communicates with a kernel component and injects itself into a system process running with root privileges.
GTIG tracked the implant under the name PLASMAGRID.
Unlike typical surveillance implants that prioritize messaging or location tracking, the payload focuses on financial data extraction. The malware scans device files and images for cryptocurrency recovery phrases and financial records.
The implant analyzes text stored in applications such as Apple Memos and searches for keywords including “backup phrase” and “bank account.” If the malware finds relevant data, it transmits the information to attacker-controlled servers.
The system also contains modules designed to extract information from multiple cryptocurrency wallet applications. Targeted apps include MetaMask, Uniswap, Exodus Wallet, and Phantom Wallet.
Investigators found that the payload could download additional modules from remote servers. These modules arrive in encrypted archives protected by hard-coded passwords.
Exploit circulation raises concerns about spyware reuse
GTIG noted that Coruna’s lifecycle shows how advanced exploits can circulate between different threat actors. The framework appeared first in surveillance operations, then espionage campaigns, and later in financially motivated attacks targeting cryptocurrency users.
The spread of the toolkit suggests the existence of an active market for reused or “second-hand” zero-day exploits.
Some researchers outside Google have debated the possible origin of the exploit kit. iVerify co-founder Rocky Cole told WIRED that the code shows signs of highly expensive development and resembles tools previously attributed to U.S. intelligence programs.
However, experts from Kaspersky told The Register that they found no direct evidence linking Coruna’s code to earlier government-associated exploits.
Users urged to update iPhones
GTIG added all known domains and websites involved in the attacks to Google Safe Browsing to reduce further exposure.
The researchers emphasized that the exploit kit fails against the newest versions of iOS. They advised users to install the latest updates. Devices unable to update should enable Lockdown Mode, a security feature that restricts functionality to defend against sophisticated attacks.
The case illustrates the growing overlap between mobile exploitation frameworks and cryptocurrency theft campaigns. Smartphones now hold sensitive financial data, which increases their value as targets for advanced cybercrime.
Disclaimer: All materials on this site are for informational purposes only. None of the material should be interpreted as investment advice. Please note that, despite the nature of much of the material created and hosted on this website, HODL FM operates as a media and informational platform, not a provider of financial advisory services. The opinions of authors and other contributors are their own and should not be taken as financial advice. If you require advice, HODL FM strongly recommends contacting a qualified industry professional.